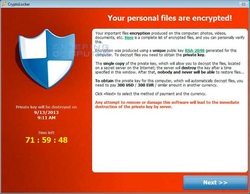
 Cryptolocker is a form of ransomware that encrypts data on the infected computer, rendering the files unreadable without the decryption key. Affected users are prevented with a screen with a countdown timer informing them that unless they pay the ransom for their data in a certain number of hours, the decryption key will be deleted. Initial Infection: The initial infection is usually received via an email attachment or "drive-by" download on an infected website. Once installed, the malware contacts its "command and control" center for instructions, which provides the malware with the encryption key and its list of targeted file types. Repair: While the infection itself can be removed without much difficulty by qualified IT professionals, without the decryption key, restoration of the encrypted data is impossible. Without paying the ransom, there is no way to obtain the decryption key, and due to the large key size, brute force decryption techniques are generally considered impossible. Early versions of Cryptolocker could be circumvented with a good system restore point, but later versions also encrypt or delete the pre-existing restore points, rendering that repair option useless. Aside from paying the ransom, the only reliable way to recover encrypted data is from a good backup of the user files. Prevention and Remediation: While there are no guarantees in regards to malware, having a reliable and up-to-date antivirus program running on a computer can help prevent the initial infection by Cryptolocker malware. Similarly, utilizing a high-quality firewall or network monitoring service that prevents the malware from contacting its command and control center can stop an infected machine from receiving its encryption key and instructions. Finally, if an infection with Cryptolocker does occur, having a reliable backup of critical information, or (even better) a disk image to restore from is the only way to recover data lost to encryption. InfinIT Technology Group offers Managed Antivirus ($3/device/month), 24/7 Remote Monitoring ($3/device/month), and Web Protection & Content Filtering Services ($3/device per month), or bundle all three services for $7/device/month. InfinIT can also help design a local backup strategy, make a baseline disk image, or set up an offsite backup for customers interested in protecting their most important data.
2 Comments
10/18/2023 05:44:39 am
Incredible insights into the world of Infinit Technologies! Their commitment to cutting-edge technology is commendable. Your post has made me even more excited about what the future holds. <a href="https://infinit-technologies.com/"> infinit technologies </a>
Reply
Leave a Reply. |
Bret FunkCompTIA A+ Certified Technician Archives
July 2016
Categories
All
|

 RSS Feed
RSS Feed