|
From Techdirt.com:
The chief judge of FISC, Reggie Walton, who has reacted angrily in the past to the claims of FISC being a "rubber stamp", has now admitted that the FISC really can't check on what the NSA is doing and relies on what they tell him to make sure that they're not breaking the law. “The FISC is forced to rely upon the accuracy of the information that is provided to the Court,” its chief, U.S. District Judge Reggie Walton, said in a written statement to The Washington Post. “The FISC does not have the capacity to investigate issues of noncompliance, and in that respect the FISC is in the same position as any other court when it comes to enforcing [government] compliance with its orders.”
0 Comments
Some of the assumptions at the heart of cryptographic theory may be wrong, which could have significant ramifications on how secure our encrypted data actually is. Does that mean your data isn't safe? Not necessarily. But it does mean that the formerly "impossible to break" encryption we use may now be just "very difficult to break".
Given that the alternative is no encryption, and given that the government (and others) already have legal access to a fair amount of our cloud-based data, this may not be the most pressing privacy concern out there. But if information theory and encryption is something that interests you, follow the previous link to read the full article from MIT, or jump straight to the scientific paper on the matter. NOTE: Follow the second link may set off your Nerd Alert alarms.  I suspect few of you knew of the existence of a Smart Toilet. The Japanese SATIS is "a cutting-edge toilet with advanced electronics technology." Owners can expect their throne to open automatically upon arrival, play music while you "work", then flush and close the lid based on your movement. The SATIS deodorizes automatically, has dedicated front and rear cleansing nozzles, and the bidet also features a "massage feature" for a truly unique potty experience. Unfortunately, due to a Bluetooth vulnerability, the SATIS can be hacked, and attackers could unexpectedly open and close the lid, flush the toilet constantly, turn the music or lights on or off at will, or even activate the bidet jets at what may prove to be an inopportune time. A hacked SATIS could significantly run up an owner's electric and water bills, but I would think that if you can pay over $4000 for a toilet, you can afford the extra water. Ever wonder how to make your "alone time" a little more special? Watch this promotional SATIS video to see what you never knew you were missing!  From Extremetech: Providing us with a delightful glimpse of the future of humanity and bionic implants, Second Sight — the developer of the first bionic eye to receive FDA approval in the US — is currently working on a firmware upgrade that gives users of the Argus II bionic eye better resolution, focus, and image zooming. The software update even provides users with color recognition, even though the original version of the device only provides black and white vision. We recently received a request from a customer to expand upon the benefits of our Basic Monitoring service.
Basic Monitoring is the first level of proactive maintenance services offered at InfinIT Technology Group. It puts the infrastructure in place for our technicians to monitor computers for problems, as well as remote repair tools to help us resolve any issues that arise quickly and with less inconvenience to our customers. Basic Monitoring Agreements do not include any pre-paid labor, but customers with a monitoring agreement get a discount on all labor charges (onsite, in-house, or remote). Cost: $5/computer/month Basic Monitoring Agreements include the following benefits:
Since reliable for-fee antivirus can cost between $30-$60 per year, a Basic Monitoring Agreement will virtually pay for itself even if you never need to take advantage of the discounted labor rates. One other advantage a Basic Monitoring Agreement offers is the ability for customers to pose questions about messages, pop-ups, or suspicious behavior on a computer to their Technical Team. With our monitoring tools, we can log in to quickly see what is causing our customers concern, and let them know whether or not a particular issue actually requires a repair. Without a monitoring agreement, customers have to pay for a service call to have those error messages looked at. This sometimes results in customers paying for a service call when none was actually required; it also sometimes results in customers ignoring issues that should be addressed because they don't want to waste money on an issue that was not a serious one. Residential and business technology needs and configurations are becoming more complex all the time. A Basic Monitoring Agreement allows our customers to take control of their networks, and turns their IT management from reactive (where we wait for a problem to occur and then try to find a way to fix it) to proactive (where our goal is to look for potential problems and address them before they cause serious issues.) If you would like more information about our Monitoring Services, please call our office at 225-286-4108, or add your comments to this post. 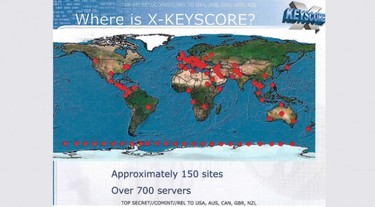 From Extremetech via the Guardian newspaper: From Extremetech: "If you were shocked by the NSA’s Prism program, hold onto your hat: The NSA also operates another system, called XKeyscore, which gives the US intelligence community (and probably most of the US’s Western allies) full access to your email, IMs, browsing history, and social media activity. To view almost everything that you do online, an NSA analyst simply has to enter your email or IP address into XKeyscore. No formal authorization or warrant is required; the analyst just has to type in a “justification” and press Enter. To provide such functionality, the NSA collects, in its own words, “nearly everything a typical user does on the internet.” Perhaps most importantly, though, it appears that HTTPS and SSL might not protect your communications from being snooped on by the NSA." Here is a link to the NSA slideshow discussing Xkeyscore While this system may not actively seek out the identity of an individual, according to slide 12 it does index "every email address seen in a session", "every file seen in a session", "every phone number seen in a session", and "the webmail and chat activity to include username, buddylist, machine specific cookies", etc. Anyone who believes that very specific information could not be gathered on an individual just from the metadata in such communications is deceiving themselves, and this program seems to go far beyond gathering just metadata. Worse (or better, I suppose, if you are a security analyst and not a private citizen concerned about your own privacy), slide 17 highlights some of the uses for XKeyscore, such as: "Show me all the VPN startups in country X, and give me the data so I can decrypt and discover the users" and "show me all the exploitable machines in country x". Now, the first of those sounds like this program can identify secure traffic on the Internet, and then help the user decrypt it, which makes me wonder just how secure our standard "best practice" Internet security is. The second is arguably more serious. It implies that the XKeyscore program can identify all computers in a target area that can be attacked by a specific bit of code (virus, malware, keylogger, etc.) and more than likely automatically take care of distributing that exploit. Perhaps not a terrible thing if good people are only using this in a very targeted way against very bad people, but if the "good guys" can do it, then other people can probably figure out how to do it too, if they haven't already. Regardless of whether you believe Edward Snowden did the right thing or the wrong thing, and regardless of whether or not you believe the US Government (and whatever other governments have access to similar programs) will only use these kinds of "powers" responsibly and for the greater good, the very existence of such capabilities should give us all cause for concern. At best, programs like Xkeyscore and PRISM (and who knows how many other similar but differently-named projects exist out there... we all watched or read the Jason Bourne stories, right?) could inadvertently provide governments with information that they should have no rights to. At worst... Well, I'd rather not dwell on a worst case scenario here. This seems like the kind of issue that should have Civil Rights and Privacy Rights advocates joining forces, demanding more information and at least requiring some real and legitimate oversight in hopes of ensuring these types of information-gathering programs are used only in the way their designers claim they are intended. Of course, that would require something to happen in Congress. Maybe the NSA has designed a program that prevents them from accomplishing any meaningful work.  Though I'm sure we were all hoping for something a little more stylish, the era of the flying car (or roadable aircraft, as it's designers prefer) may finally be upon us. MIT startup Terrafugia has been showcasing its Transition vehicle, a 2-seat aircraft that can fold its wing to become a road-ready automobile. The transition runs on unleaded gas, has a flight range of 500 miles, an airspeed of ~110mph, and a road speed of 70mph. With the prototype costing around $300,000, the Transition may not be for everyone. But it's a start. |
Bret FunkCompTIA A+ Certified Technician Archives
July 2016
Categories
All
|

 RSS Feed
RSS Feed