 Following their recent acquisition of Nest, Google has purchased the company that makes Dropcam, a streaming webcam/security camera and associated Cloud Service. The Interface is slick and simple, the devices and services are reasonably priced, and there's a lot of peace-of-mind that such an offering can provider. However, as Extremetech points out, "Just imagine what Google could do with a real-time, high-res video feed of your home. Where the Nest thermostat might give Google some behavioral data — how warm/cold you like the house, your comings and goings — it pales in comparison to Dropcam. With Dropcam, Google would know exactly what you’re up to at any given time. If you’re preparing dinner, Google Now might automatically prompt you with “tips on how to make the perfect souffle.” If you’ve just brought a newborn baby back from the hospital, you might suddenly find lots of Google ads for diapers and strollers. If it hears you shouting at your game console, it might tailor your search results to show some different, less-antagonizing games." We tend to fall more into the "Google is helpful" rather than the "Google is evil" category, but I have concerns about systems such as this and the current generation of gaming consoles, which is constantly streaming data off to some server somewhere else, with the only thing protecting me from how that data is used being the privacy policy that I didn't read and likely wouldn't understand in its nuanced legalese. Moreover, even if Google can be trusted, recent events have shown that once data is online, it can be hacked, and I'm not certain how comfortable I'd be with 7-30 days of my comings and goings available online for a would-be thief to study prior to breaking into my house. Then again, this line of work has gone a long way to making me paranoid. So perhaps I'm overreacting. That Nest smoke detector does sound nice...
1 Comment
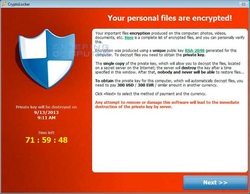 Cryptolocker is a form of ransomware that encrypts data on the infected computer, rendering the files unreadable without the decryption key. Affected users are prevented with a screen with a countdown timer informing them that unless they pay the ransom for their data in a certain number of hours, the decryption key will be deleted. Initial Infection: The initial infection is usually received via an email attachment or "drive-by" download on an infected website. Once installed, the malware contacts its "command and control" center for instructions, which provides the malware with the encryption key and its list of targeted file types. Repair: While the infection itself can be removed without much difficulty by qualified IT professionals, without the decryption key, restoration of the encrypted data is impossible. Without paying the ransom, there is no way to obtain the decryption key, and due to the large key size, brute force decryption techniques are generally considered impossible. Early versions of Cryptolocker could be circumvented with a good system restore point, but later versions also encrypt or delete the pre-existing restore points, rendering that repair option useless. Aside from paying the ransom, the only reliable way to recover encrypted data is from a good backup of the user files. Prevention and Remediation: While there are no guarantees in regards to malware, having a reliable and up-to-date antivirus program running on a computer can help prevent the initial infection by Cryptolocker malware. Similarly, utilizing a high-quality firewall or network monitoring service that prevents the malware from contacting its command and control center can stop an infected machine from receiving its encryption key and instructions. Finally, if an infection with Cryptolocker does occur, having a reliable backup of critical information, or (even better) a disk image to restore from is the only way to recover data lost to encryption. InfinIT Technology Group offers Managed Antivirus ($3/device/month), 24/7 Remote Monitoring ($3/device/month), and Web Protection & Content Filtering Services ($3/device per month), or bundle all three services for $7/device/month. InfinIT can also help design a local backup strategy, make a baseline disk image, or set up an offsite backup for customers interested in protecting their most important data. |
Bret FunkCompTIA A+ Certified Technician Archives
July 2016
Categories
All
|

 RSS Feed
RSS Feed